Powerpoint is the world s most popular presentation software which can let you create professional mobile threats attacks powerpoint presentation easily and in no time.
Mobile security threats ppt.
2015 check point software technologies ltd.
Slideshare uses cookies to improve functionality and performance and to provide you with relevant advertising.
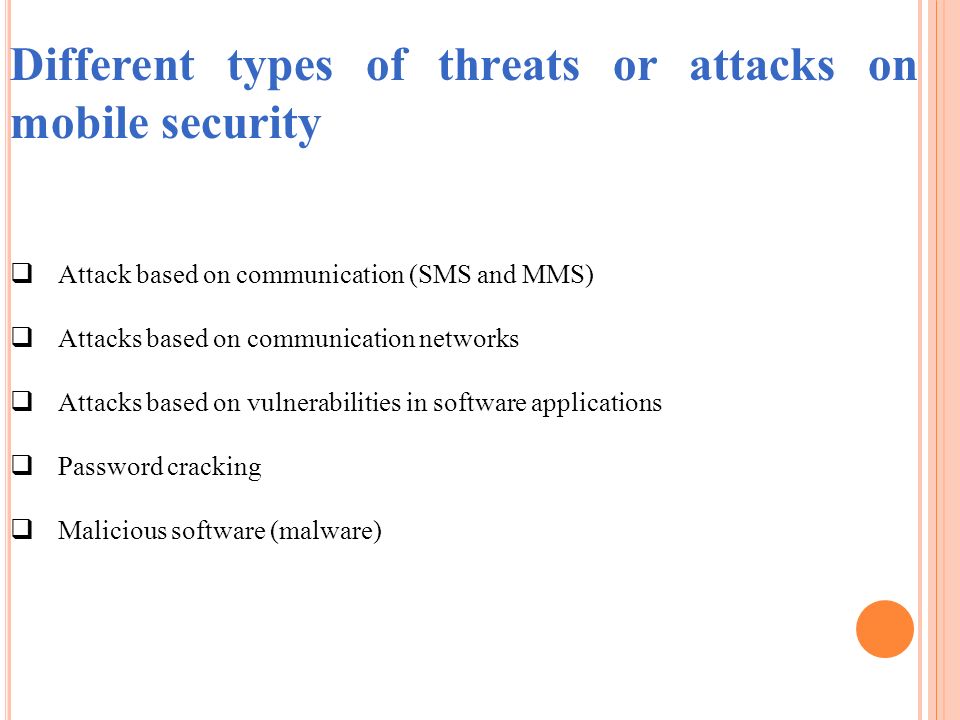
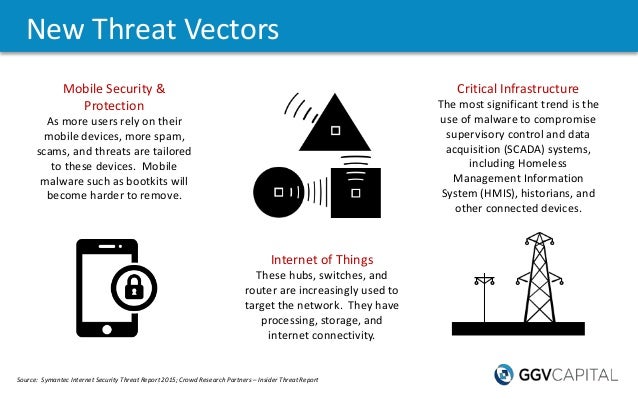
Common mobile malware hijack browser sessions spy on user activities display false misleading adware and open communications to a remote attacker.
Apts target individuals businesses governments and their data and redirect it via mobile connections.
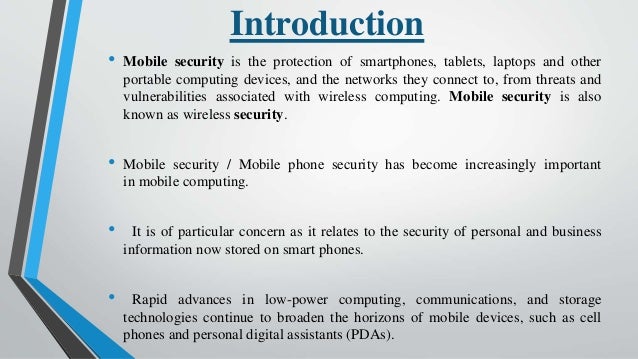
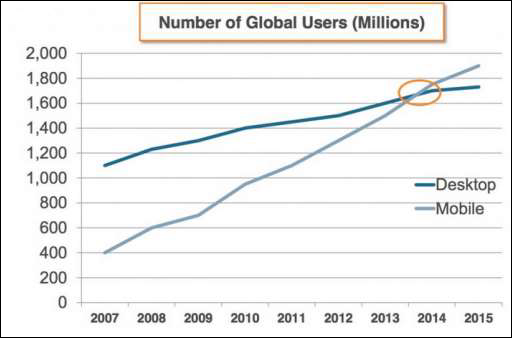
Smartphones popularity and relatively lax security have made them attractive targets for attackers.
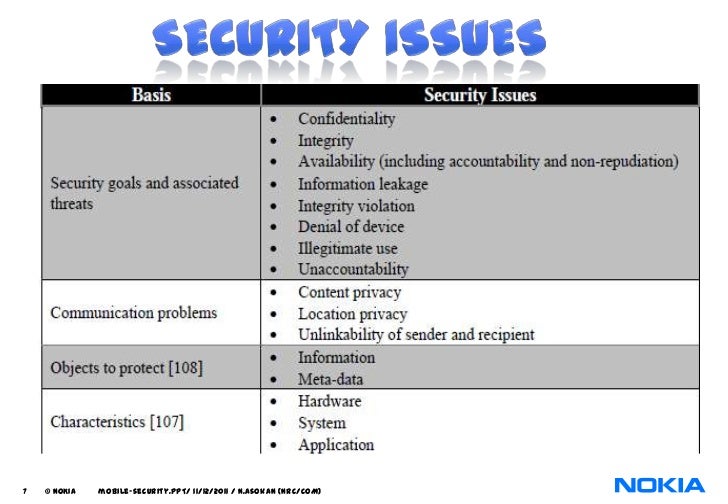
These threats can disrupt the operation of the smartphone and transmit or modify user data.
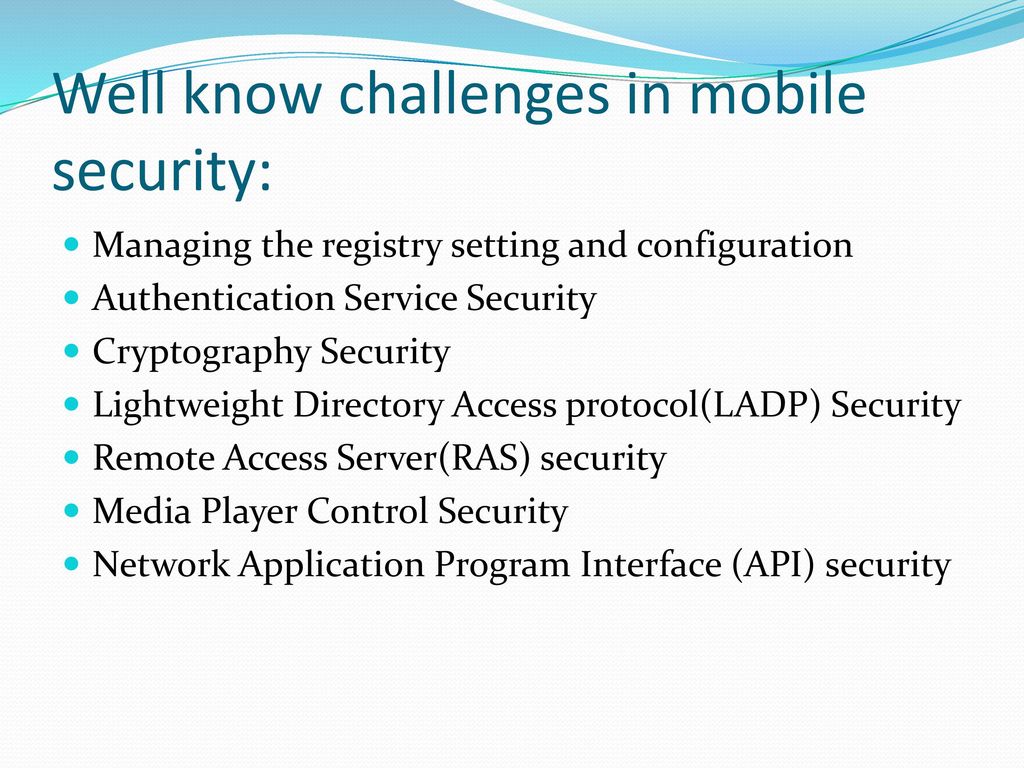
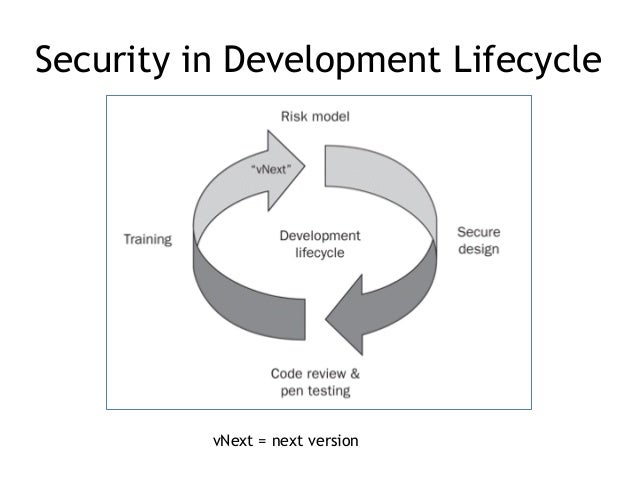
Even within the mobile ecosystem hbr reported that security spending was chronically underfunded relative to mobile app development.
If you continue browsing the site you agree to the use of cookies on this website.
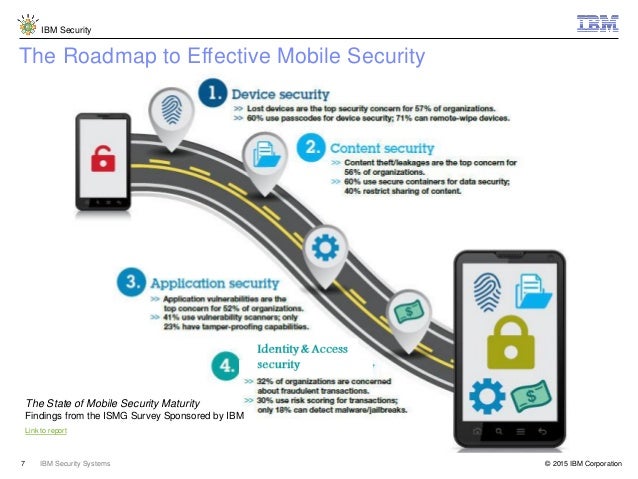
But the bottom line is that it s no longer about the device.
Spyware is a type of malware that infiltrates your device to damage your computer or to gain access to your sensitive information often without your knowledge.
Threats in mobile and it s security.
Mobile security threats that can affect both android and apple devices spyware.
Challenges of smartphone mobile security threats.
In just the last two quarters of 2012 the number of unique mobile threats grew by 261 according to abi research.
According to harvard business review hbr despite becoming a preferred target for hackers mobile security is not prioritized relative to network and computer security.
Spyware gathers your personal information and relays it to advertisers data firms or external users.
Advanced persistent threats apts.
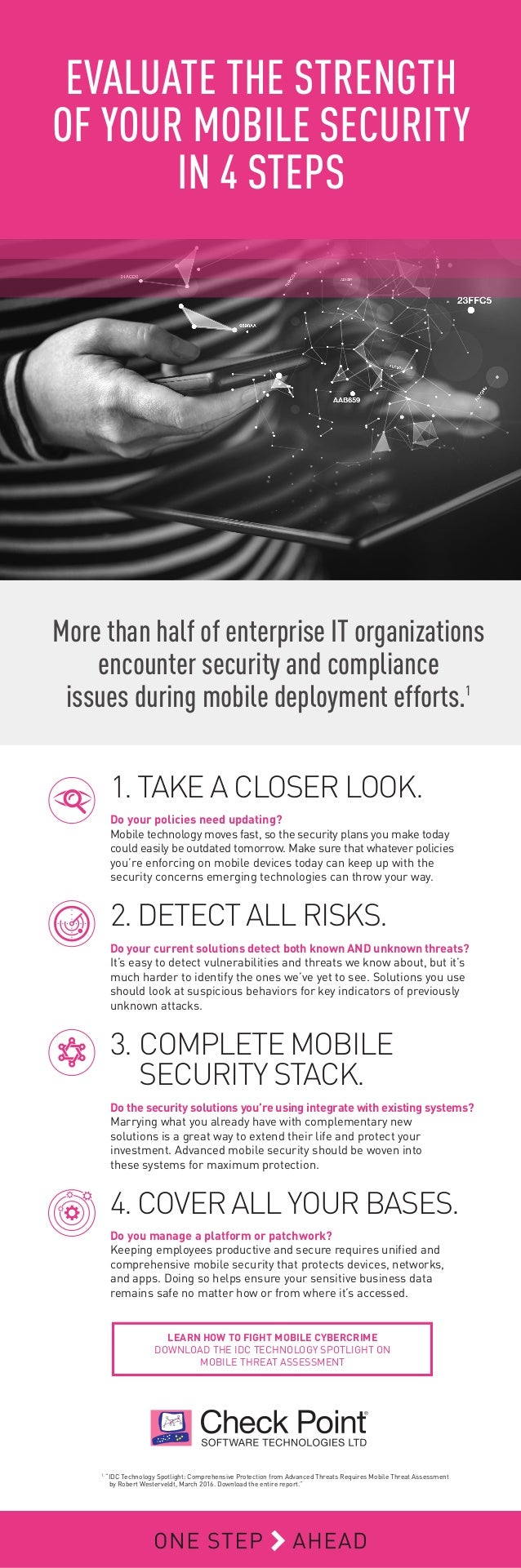
31 taking mobile security beyond mobile threat prevention restricted only for designated groups and individuals mobile threat prevention threat prevention for mobile devices capsule cloud protect laptops when off the business network capsule workspace docs protect business data on mobile devices.
Tis the season for mobile threats.
One of the most dangerous examples of stealth.
This helps you give your presentation on mobile threats attacks in a conference a school lecture a business proposal in a webinar and business and professional representations.
John maddison mobile security.
What s next in mobile security threats.
The uploader spent his her valuable time to.
A smartphone user is exposed to various threats when they use their phone.
Applying a zero trust model to mobile and the right security controls at the app level could align productivity and security.